We’re interrupting the Ultimate Guide to PCI DSS Requirement Frequencies to bring you an important lesson on how to decipher the requirements in the DSS.
Who should read this post: PCI ISA’s, PCI-P’s, PCI QSA’s or anyone who just got tagged by their boss to run their PCI Compliance program.
Before we take a deeper dive into the anatomy of PCI requirements, let’s revisit some important requirement characteristics. Understanding these characteristics will help you dissect the requirements as you assess your cardholder data environment.
Six important characteristics of PCI DSS requirements include (but not limited to):
- If you’re being assessed for the full PCI DSS, there’s over 400 requirements and sub-requirements that you must be in compliance with to pass your annual Report on Compliance. Not all of these requirements may apply to your environment. You will need to work with your QSA to determine what is “not applicable.”
- Each main requirement may have one or many sub-requirements that may have one or many testing procedures that may have one or many burdens of proof.
- Some requirements are repetitive, contradictory, and / or no longer seen as a best security practice.
- Requirements have frequencies, which means that compliance is ongoing and must be continuous for merchants to remain in good standing with their legal and contractual obligations.
- Some requirements loop together, which means that if you fail one, you may be failing all the requirements that loop together.
- If you can’t comply with a requirement there are only two ways around it:
- Your acquirer accepts the risk.
- You implement a defensible compensating control.
Now let’s dive into the anatomy of the PCI DSS requirements!
4 Key Ingredients You Must Understand to Be Compliant

- The requirement
- The testing procedure
- The intent of the requirement
- The proof required to validate your compliance
The PCI DSS Requirements
Think of the DSS as the skeleton or the structure of your PCI Compliance program. The requirement tells you what you need to comply with.
The Testing Procedures:
The testing procedures make up part of the connective tissue surrounding the structure of the requirements. The testing procedures tell you how to comply with the requirement. Be careful here as the testing procedures don’t always match up with the proof you need to fully satisfy your compliance.
The Intent of the Requirement
The intent of the requirements is more connective tissue that connect the requirements and testing procedures. The intent tells you why you must comply. The PCI DSS includes this with the requirements to help explain the rationale and better educate merchants about securing their payment card environments.
The Proof Required to Validate Your Compliance
Here’s where it gets interesting. The proof required to validate your compliance is not in the PCI DSS. It’s in the Requirements and Security Assessment Procedures.
Say what?
I remember what it’s like moving from self-assessing to conducting the annual Report on Compliance for the first time. I was hired as a project manager to run several concurrent IT projects to implement security monitoring of the company’s cardholder data environment. These tools that didn’t exist when the company was self-assessing. It took nearly two years to get that first Report on Compliance and it was agony. Nobody knew about the Requirements and Security Assessment Procedures.
Way back in 2012, I did a little digging on the PCI SSC website and I found this little gem of a document. I recall standing in front of an IT Security director and showing him everything we needed to do to prove our compliance. It was eye opening to say the least.
When I became the company’s PCI ISA, I had to redirect a Fortune 100 company that was used to simply answering “yes” or “no” or “N/A” on the SAQ-D to proving compliance with documentation that didn’t exist. It was like herding cats.
Of course, once we created the standards, process, procedures, and implemented the right security tools, the PCI DSS version changed from 2.0 to 3.0 and it was back to the drawing board for a number of gaps. I’ll leave that for another blog post because if you haven’t heard, version 4.0 will be published in early 2022.
Let’s Break It Down
In the first image we have requirement 10.2 and its first two sub-requirements. You can see the requirement, testing procedure, and guidance for each.
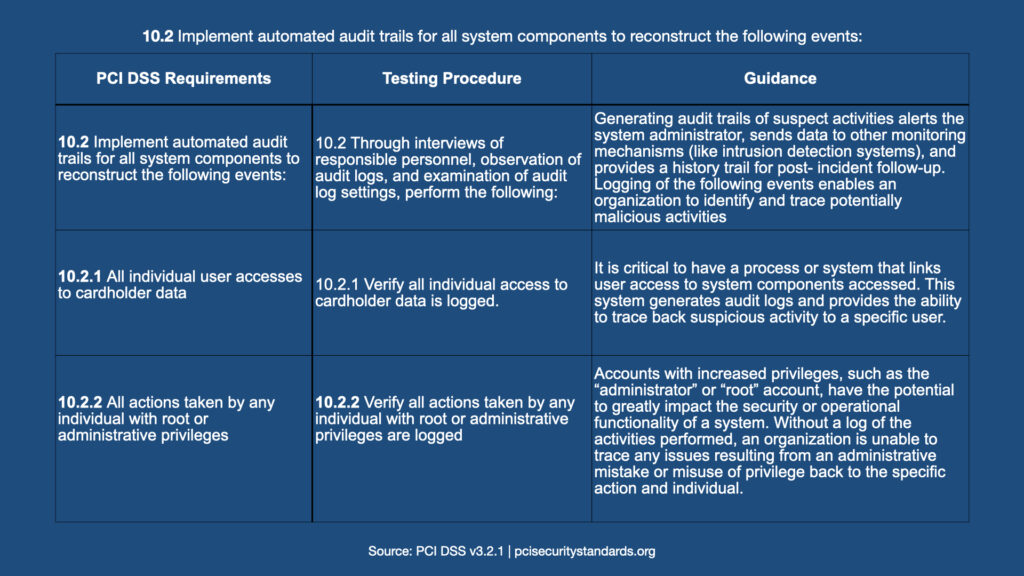
How would you verify compliance with both sub requirements? What would you provide to your QSA as proof?
Now take a look at the second table.
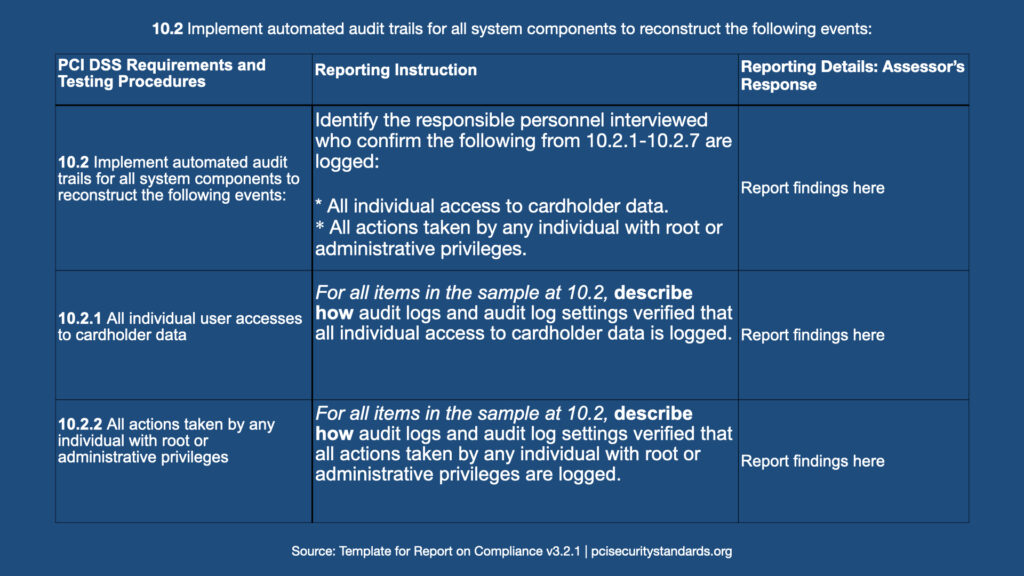
What evidence would you provide now?
As you can see with this example, whether your company is self-assessing or completing a Report on Compliance, you need to understand both the current version of the PCI DSS and the current version of the Requirements and Security Assessment Procedures. And if your company is a level 2 merchant about to tip over 6 million transactions and become a level 1 merchant, Payment Card Assessments highly recommends getting to know the Requirements and Security Assessment Procedures intimately.
If you’re still pulling out your hair trying to understand what your company needs to do to be PCI DSS compliant, reach out and request a call back. Your first 30 minute consultation with Payment Cards Assessments is free!
We can help. Request a call back today!
Upcoming Events
Ask Us Anything
Ask Us Anything (About PCI) is a FREE live online event. Once you register and confirm, you’ll be sent the zoom link for this lively chat!
Click the image to register today.
Assess Smarter Not Harder
Saving $92,000 in outside QSA assessment fees isn’t always easy, but with the right tools and framework, you can build a complete and functional PCI DSS Compliance program that not only saves you time, money, and effort; but also makes it easier for your QSA to assess your cardholder data environment. Led by two PCI DSS Compliance experts with over 20 years of combined experience, this 60 minute seminar will guide you through our successes and challenges with a complex and complicated cardholder data environment.
3 Key Takeaways:
1. Learn how pinpoint and remediate key issues before your annual Report on Compliance.
2. Master how to revise and enhance critical compliance processes to show maturity in your compliance program
3. Take away actionable steps on how to create a sustainable PCI DSS compliance program that saves time and money in outside QSA assessment fees.
This session will be 50-60 minutes long with time at the end for Q/A.
1 CPE will be awarded for attendance.
Date & Time:
Tuesday, October 5th, 2021
12:00pm – 1:15pm EST
Where:
Zoom (info will be emailed upon registration confirmation)
Price: