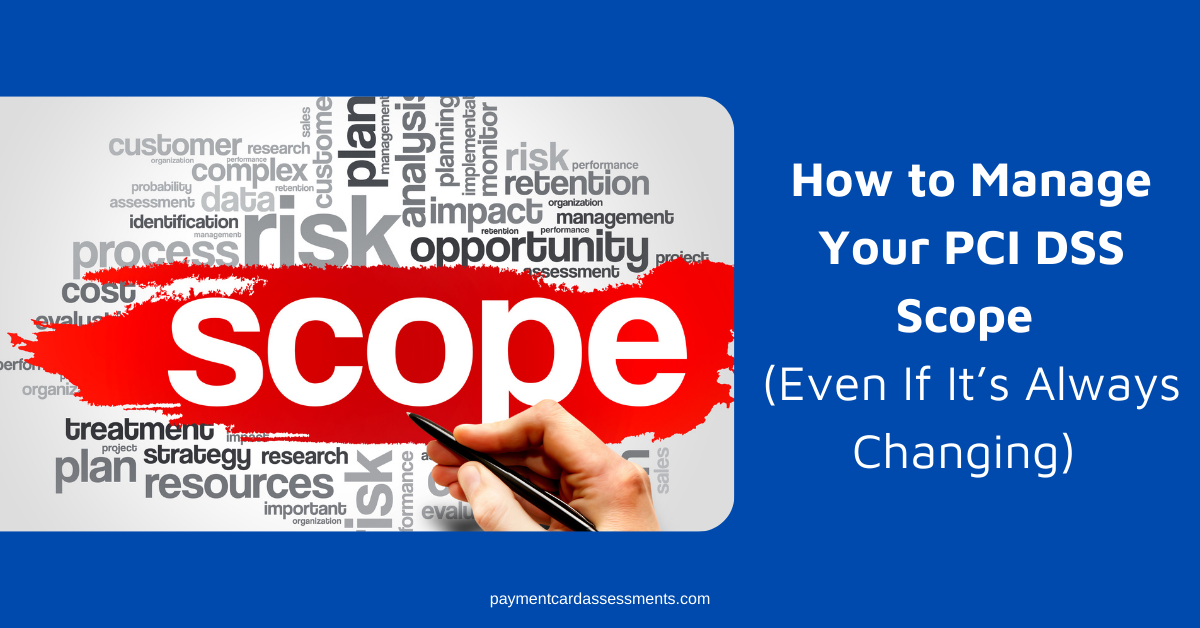
Before we dive into our Ultimate Guide On How To Manage PCI DSS Requirement Frequencies, a bi-monthly blog series, it’s critical that we start with scope. Why? Understanding and knowing your scope is where you begin to create, build, and maintain a continuous PCI DSS Compliance program. If you don’t have a firm grasp on what’s in scope for assessment, being able to complete a self-assessment or, if you’re a level 1 merchant, a mandatory Report on Compliance is next to impossible.
Per the PCI DSS,
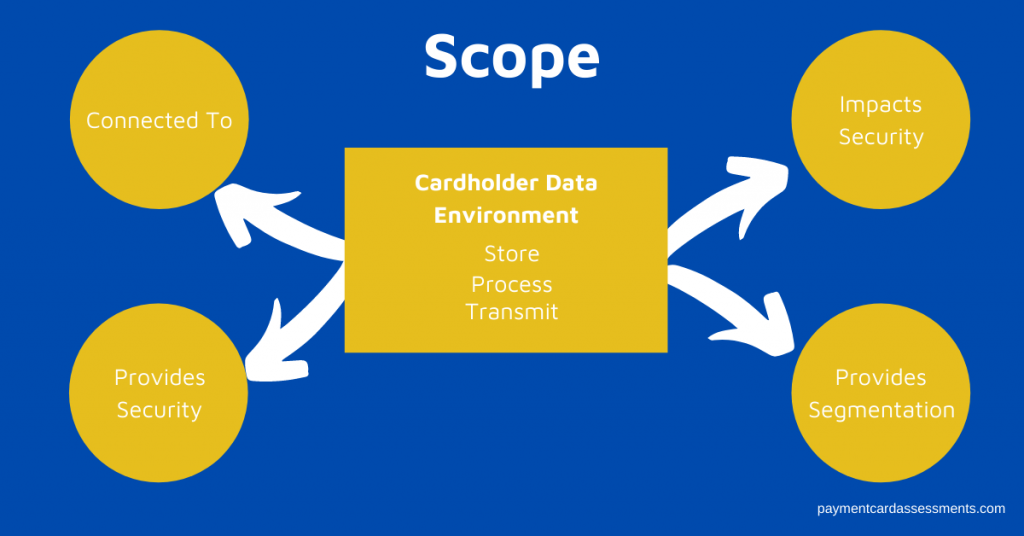
“The PCI DSS security requirements apply to all system components included in or connected to the cardholder data environment. The cardholder data environment (CDE) is comprised of people, processes and technologies that store, process, or transmit cardholder data or sensitive authentication data. “System components” include network devices, servers, computing devices, and applications.
www.pcissc.org
Furthermore, the PCI SSC Information Supplement: Guidance for PCI DSS Scoping and Network Segmentation states that the following scoping concepts always apply:
Systems located within the CDE are in scope, irrespective of their functionality or the reason why they are in the CDE.
Similarly, systems that connect to a system in the CDE are in scope, irrespective of their functionality or the reason they have connectivity to the CDE.
In a flat network, all systems are in scope if any single system stores, processes, or transmits account data.”
www.pcissc.org
And last but not least, PCI DSS requirement 2.4 requires merchants to
“maintain an inventory of system components that are in scope for PCI DSS.”
PCI DSS v3.2.1
Does Managing Your PCI Scope Feel Like You’re Herding Cats or Trying to Nail Jell-o to a Tree?
If you don’t have a handle on your scope, achieving or maintaining PCI DSS Compliance is next to impossible.
I remember when I stepped into my role as a PCI ISA for a level 1 merchant. Our asset inventory wasn’t on just one excel spreadsheet but six. I had no idea which one was the right one and our asset management team responsible for all assets had no way of identifying what was a PCI asset.
Crazy, right? We literally had no process to properly identify scope. In fact we over-scoped and included things that didn’t meet the definition of scope as defined by the PCI DSS. That first PCI Report on Compliance in 2012 was a nightmare.
What did we do? As the PCI Compliance & Sustainability team, we took ownership of the PCI in scope asset list and we created best practices and processes around our scope.
6 Simple Ways to Oversee Your PCI In Scope Assets Through Process Improvement and Automation
Step 1: Start at the beginning. People, process, and technologies are in scope for assessment if they are in the direct path of processing, transmitting or storing payment card data. Once you’ve identified everything in the direct path of the card flow, go to Step 2.
Step 2: Identify all people, processes, and technologies that are connected to the direct path of the card flow. Identify all the technologies that are used to provide network segmentation and / or could impact the security of the cardholder data environment.
Step 3: Create an inventory of all your people, processes, and technologies that are in scope for PCI DSS assessment.
Step 4: Confirm these inventories frequently. Best practice frequencies that we recommend:
- Cardholder data flows and payment processes – Quarterly
- People (department codes, subject matter experts, control owners, vendors, etc) – at least every six months.
- Technologies – While security technologies may not change frequently, upgrades to them will occur. These upgrades will need to be updated in your inventory. We recommended a quarterly frequency to keep your technology inventory updated.
- Physical Assets – Hardware/Software that’s used in the cardholder data environment – these change regularly. Hardware assets get upgraded, decommissioned, or added to the production environment. We recommend a weekly reconciliation of physical assets.
Step 5: Automate the process to keep the physical asset inventory as accurate as humanely possible because as you will learn in future articles, many PCI DSS requirements will be applied to these assets.
Step 6: As a best practice, we highly recommend a full scope review at least twice a year.
- 30 days before a PCI Report on Compliance – confirm everything from your physical assets to your subject matter experts and everything in-between that meets the PCI DSS definition of scope. An accurate inventory is required to both pull sample sets and to also meet PCI DSS requirement 2.4. Be sure to read our article, “How Well Do You Know Your PCI Assets.”
- An interim scope review 6 months after your most recent PCI DSS Report on Compliance is completed.
How Are You Managing Your PCI Scope?
- Do you have processes in place to manage changes to your cardholder data environment whether it’s people, processes or technology?
- Do you know who your subject matter experts and control owners are?
- If you were asked today for your in-scope inventory, would you feel confident in its accuracy?
If you’re having trouble answering those three questions, you’re not alone. We’ve been there. And we can help. Request a call back today and receive a free 30 minute consultation to see if partnering with Payment Card Assessments is right for you!
We’ve added a Scope Review Checklist to our Toolkits. Be sure to register for access and you’ll also receive our Firewall Review Checklist, Interview & Observation Prep Checklist, and our Physical Security Checklist.
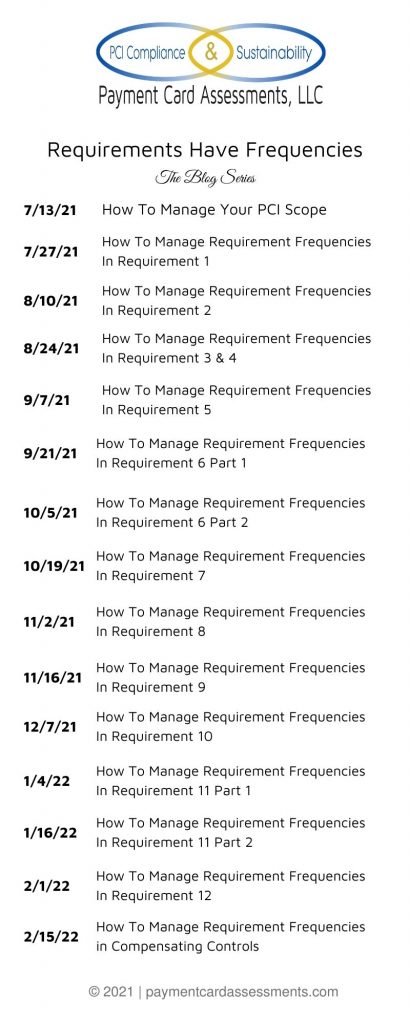
The Ultimate Guide On How To Manage PCI DSS Requirement Frequencies – Series Schedule