Welcome back to the Ultimate Guide To PCI DSS Requirement Frequencies! In the last installment we covered the critical factor of SCOPE. Now that you have a better understanding of your PCI DSS scope, let’s get started with PCI DSS Requirement 1: Build and Maintain A Secure Network and Systems.
Requirement 1 has five requirement groups and 34 sub-requirements. Of the sub-requirements, only one has an explicit frequency and two others have an implied frequency. These frequency requirements can make or break your compliance with a number of sub-requirements in this section.
Change Management
While there is no specified frequency for managing changes to firewalls and routers, your organization must have a robust change management program that includes standard procedures, formal processes for testing and approval, and the ability to maintain records of changes. During a Report on Compliance, you must be able to provide a list of all changes made in the previous six months in order for your QSA (or ISA) to pull a sample. Any and all changes made to the firewall and router configurations will be compared to the change records. If they don’t match, you will not pass.
Current Network and Cardholder Data Flow Diagrams
Both requirement 1.1.2 and 1.1.3 have implied frequencies. While the DSS does not state how often organizations must review and update their network and cardholder data flow diagrams, the word “current” means that you’re updating as often as you need to keep these diagrams current.
Best practice: Based on the complexity of your cardholder data environment, we recommend that network and cardholder data flow diagrams are reviewed quarterly and updated accordingly. Not only will this frequency keep you compliant but it will also help you identify any new scope that gets added based on changes to the environment.
Note: During a Report on Compliance, the QSA will be comparing your network diagram to your firewall configuration standards to ensure your diagram in sync with your standards.
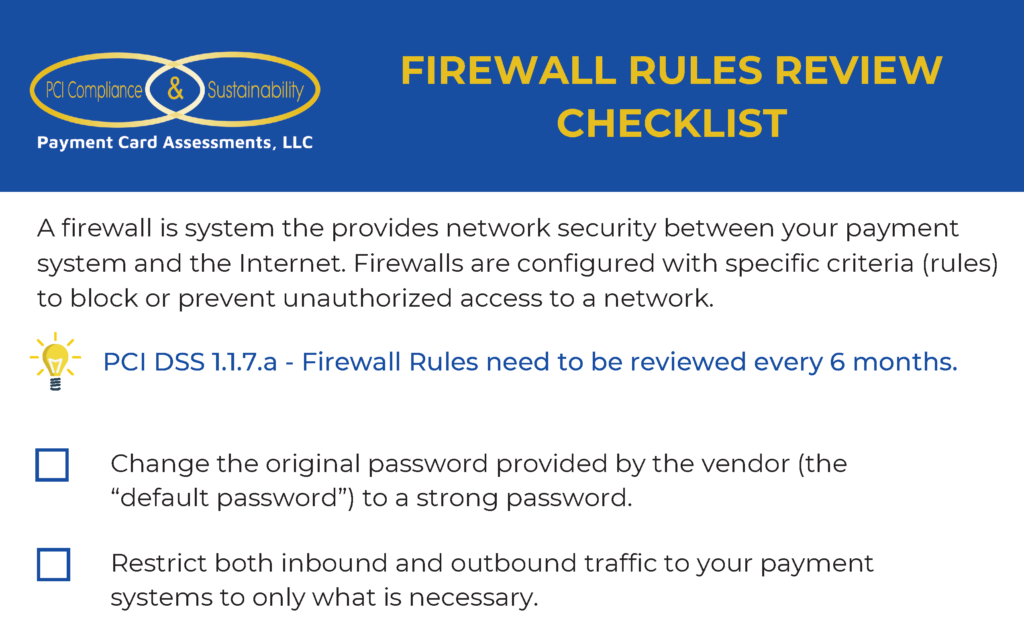
Firewall and Router Rule Sets
Requirement 1.1.7 has a specific frequency. You are required to review your firewall and router rule sets at least every six months. For the Report on Compliance, you must have it documented either in your network security standard or firewall configuration standard that your organization requires rule sets to be reviewed every six months, you must have a report or other documentation that shows the results of your rule set reviews, and someone must verbally attest to the fact that your organization reviews rule sets every six months.
So What Exactly Are You Reviewing Every Six Months?
- Review your firewall and router configurations to ensure they restrict connections between untrusted networks and any system component in the cardholder data environment (requirement 1.2.x).
- Restrict inbound and outbound traffic to that which is necessary for the cardholder data environment and specifically deny all other traffic (requirement 1.2.x).
- Stop all direct public access between the internet and any system component in the cardholder data environment (requirement 1.3.x).
Be sure to download your FREE Firewall Rule Review Checklist!
Best Practices For Rule Set Reviews
Developers and system administrators request changes to firewall rule sets all the time. Whether it’s to do work on system components or test system components, these changes can make a mess out of your rule sets. It’s so easy for someone to unintentionally request an “any” rule which is prohibited in the cardholder data environment. Our best advice is to insert your ISA or someone on the compliance team into the firewall rule change review.
Personal Firewall Software
If your organization has deployed a personal or host based firewall solution for laptops that connect to the internet when outside the network and also connect to the cardholder data environment (example: customer service reps who work from home), the host based firewall solution as two of its own sub-requirements and must also meet sub-requirements that include change management, configuration standards, be included in the diagram(s), and rule set reviews.

Training and Education
At the end of every main requirement area there is a catch-all requirement that requires security policies and operational procedures be documented, in use, and known to all affected parties.
It’s imperative that your organization’s ISA or PCI compliance team has a strong working and professional relationship with your network security team. It is in your ISA’s best interest to help the network security team understand their PCI requirements, roles and responsibilities.
Don’t miss our next installment on PCI DSS Requirement Frequencies!
Our next article will be on PCI DSS Requirement 2: Do not use vendor supplied defaults for system passwords and other security parameters. It’s the other security parameters where we’ll be focusing on. Never miss a post by subscribing today:

Do You Require Immediate Assistance With Your PCI Compliance Program?
If you need immediate help with a current Report on Compliance or establishing a PCI Compliance Sustainability Program, request a call back today and we’ll schedule a free 30 minute consultation to see if partnering with Payment Card Assessments is right for you.